- North Korea’s Famous Chollima uses blockchain tech to hide malware in smart contracts, targeting job seekers.
- EtherHiding malware exploits decentralized blockchain, evading detection while siphoning crypto and credentials.
- Fake job recruiters trick victims with infected files, stealing funds from crypto wallets via malicious smart contracts.
North Korea’s hacking group, Famous Chollima, has come up with a nifty new online crime. They have employed blockchain tech to embed malware in Ethereum and BNB Chain-based smart contracts. This method, named EtherHiding, is the first evidence of a nation-state actor exploiting blockchain in these types of malicious operations. The group’s main targets are job seekers, masquerading as recruiters while delivering malware that filches crypto and credentials.
The EtherHiding concept leverages the decentralized characteristic of blockchain. Malware can be encoded in smart contracts and is difficult to trace or erase. The malware can be replaced by the attackers at any time, making the attack even harder to stop. This enables them to supersede classical security frameworks.
The malware reportedly gets onto computers through fake job interviews. Unsuspecting teams end up with their encrypted files held hostage by scammers who purport to be companies like Coinbase and Robinhood, luring victims into downloading infected files as part of technical assessments. After compromising a system, the malware siphons off private information like credentials and cryptocurrency.
Attackers Use Fake Chess App to Spread Malware and Steal Sensitive Data
The attacks were independently verified by Cisco Talos and Google Threat Intelligence. They discovered that the malicious software can log keystrokes and capture screenshots, recording what victims type and spying on activity. Now, hackers don’t have to try so hard and can retrieve all sorts of valuable data without anyone knowing.
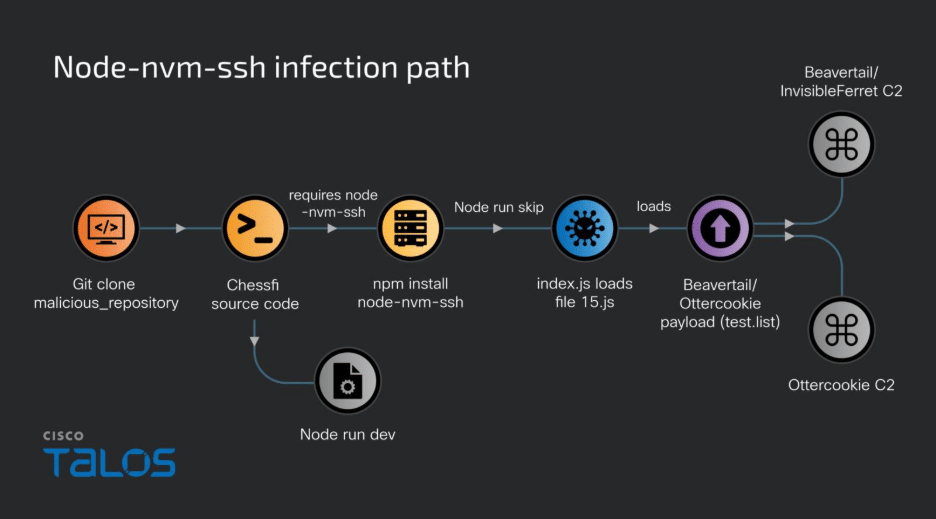
Source: Cisco Talos
The malware itself is served from a compromised Node.js package called node-nvm-ssh. It’s lurking under the guise of a chess app in the NPM repository with the name “Chessfi.” Recipients who download the compromised file unknowingly activate the malware, infecting their device.
The attackers were also connected to a group from North Korea called UNC5342, according to Google Threat Intelligence. Since the early months of 2025, the group has begun injecting JADESNOW malware and INVISIBLEFERRET backdoors into smart contracts. This method complicates efforts to counter the attacks, as these backdoors create a decentralized command-and-control network that is nearly impossible to dismantle.
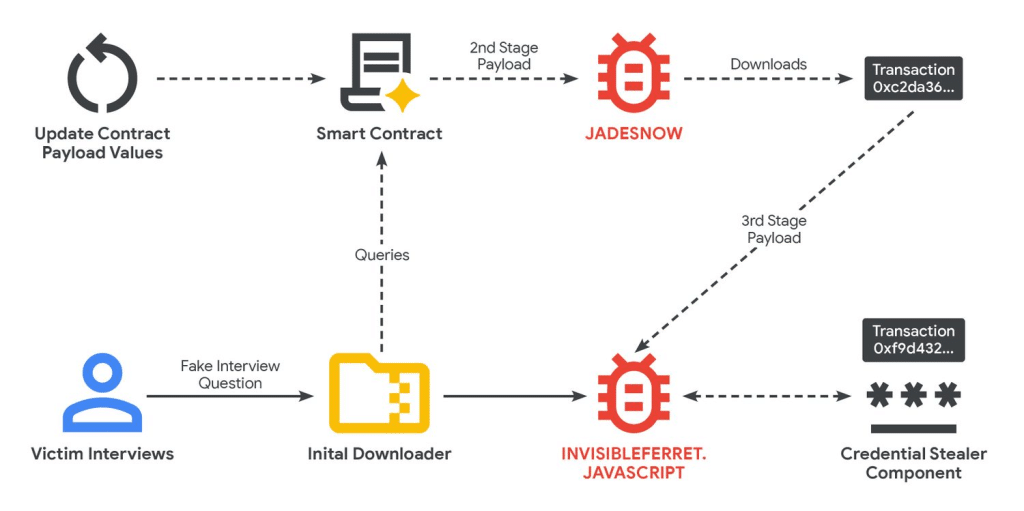
Source: Google Cloud
Also Read: Ripple Leads Industry Discussion on Stablecoin Standards and Global Regulation
North Korean Hackers Steal Billions via Blockchain
EtherHiding uploads malicious code onto smart contracts in public blockchains. This approach ensures that the malware is more difficult to detect and delete. Because blockchain technology is decentralized, there’s no central authority to knock out the bad infrastructure. The perpetrators are free to keep doing what they are doing.
The revelation comes as North Korean hackers have been extremely effective in committing cybercrime. By 2024, they had taken more than $1.3 billion in 47 attacks. By the middle of 2025, they had already stolen $2.2 billion. The money is thought to be part of a complex system that funnels funds to North Korea’s weapons program.
EtherHiding gives attackers several advantages. By the use of read-only function calls, they are able to circumvent classical transaction fees in order to fetch their malicious payloads. It is next to impossible to track the attackers, because this process does not leave any records on the blockchain.
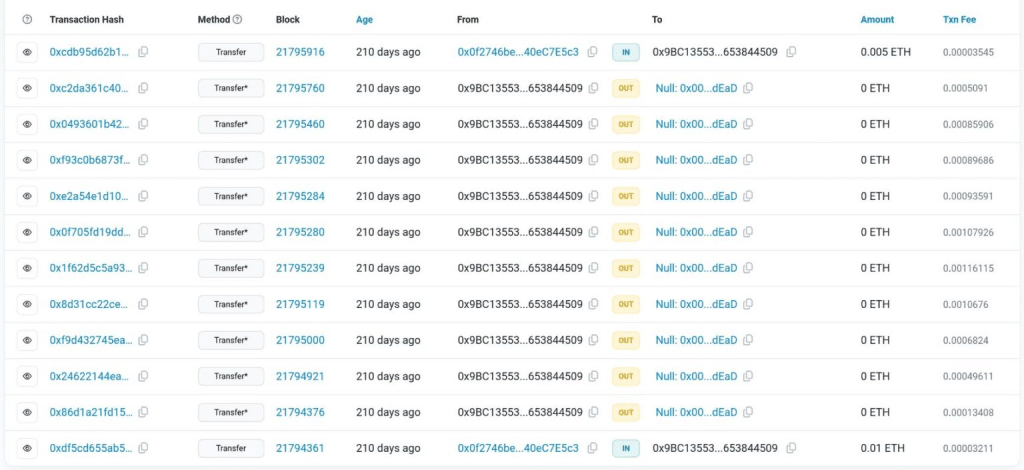
Source: Google Cloud
Fake Job Interviews Target Crypto Wallets in Contagious Interview Scam
The Contagious Interview is one of the group’s best-known operations. The fake recruiters dupe victims into downloading malicious files from GitHub repositories. The files launch a multistep infection that plants malware on the devices of victims. The malware puts its focus on more than 80 browser add-ons, which includes well-known crypto-wallets like MetaMask and Phantom, with the aim of siphoning funds directly from victims’ wallets.
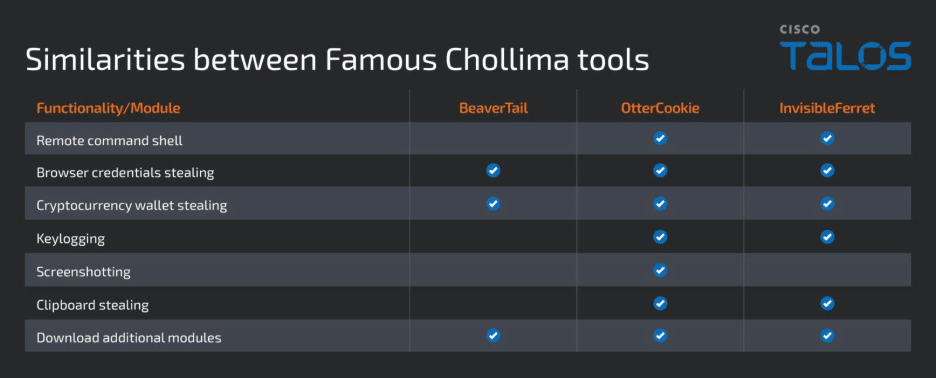
Source: Cisco Talos
North Korean agents have also established sham businesses to legitimize their activities. The attacks were attributed to companies including Blocknovas and Softglide. The bad actors utilize the bogus enterprises to spread malware and also gain the trust of their victims.
The increase in such attacks has prompted warnings from figures in the cryptocurrency industry. According to the CEO of Binance, Changpeng Zhao, fake job applications and fraudulent interviews continue to be prevalent threats. He also called on the industry to enhance its security measures in a bid to prevent such scams from being successful.
These North Korean hackers are advanced, creative and patient. I have seen/heard:
— CZ 🔶 BNB (@cz_binance) September 18, 2025
1. They pose as job candidates to try to get jobs in your company. This gives them a “foot in the door”. They especially like dev, security, finance positions.
2. They pose as employers and try to… https://t.co/axo5FF9YMV
U.S. officials have acted in the face of these threats. They have confiscated more than $7.7 million in cryptocurrency from networks that North Korean IT workers, part of a group known as the Lazarus Group, were using to generate money through cybercrime.
With the presumption of disassociation from both types, the threat of North Korean hackers leveraging blockchain technology for utility is still real. The attacks are evolving, and blockchain is now a key tool in their cybercrime arsenal.
Also Read: Uniswap Adds Solana Support, Expanding Access to Over 1 Million Tokens
How would you rate your experience?






